










加密技術是當今幾乎所有數位系統的核心。這是一種精密的身分辨識機制,將可讀資訊轉化為受保護的數據,確保全球範圍內的隱私、安全與合規性。
您可以將加密想像成一個高科技保險箱。為了保護您的數據,它會經過四個階段:
使用單一秘密金鑰進行加密與解密。它的效率極高且速度快,是全磁碟加密與資料庫安全的標準規格。
範例:AES, XChaCha20
使用一對金鑰:一個用於加密的 公鑰 以及一個用於解密的 私鑰。這對於網路上安全的身分驗證至關重要。
範例:RSA, ECC
加密技術不僅僅是一項安全功能,它是現代生活的基準要求:
在 NordPass,我們使用最先進的 XChaCha20 演算法 來保護您的數位保險箱。這種對稱串流加密法專為極速與強大安全性而設計,確保您的密碼、信用卡資訊和安全筆記始終處於 256 位元的嚴密保護之下。
關於 NordPass
NordPass 由領先全球網路安全產品市場的 Nord Security 公司開發。網路已成為一個混亂的空間,網路犯罪和資料保護問題損害了安全和信任。因此,我們團隊的全球使命是為世界各地的人們塑造一個更值得信賴、更和平的線上未來。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。



在現代 IT 管理中,您的支出方式與購買內容同樣重要。支出分類錯誤可能導致財務報表不準確、稅務複雜化,甚至造成策略上的盲點。
CapEx (資本支出) 指的是對實體伺服器、數據中心設備和永久軟體授權等資產的重大投資。這些成本會透過 折舊 (Depreciation) 分攤到數年內。
OpEx (營運支出) 涵蓋 IT 營運的日常成本。這包括雲端訂閱 (SaaS/IaaS)、維護合約和公用事業費用。這些費用在發生的月份即 全額列支。
| 特性 | CapEx (資本) | OpEx (營運) |
|---|---|---|
| 核心焦點 | 長期資產增長 | 持續性營運能力 |
| 會計處理 | 資產負債表 (資產) | 損益表 (費用) |
| 稅務處理 | 分 3-7 年扣除 | 當年度全額扣除 |
| 風險特徵 | 技術過時、利用率不足 | 變動成本激增 |
無論您選擇重資產的 CapEx 模型還是靈活的 OpEx 策略,可見性都是成功的關鍵。像 Atera 這樣的平台提供即時資產發現與自動化文檔記錄,協助追蹤設備生命週期與訂閱使用情況,確保您的財務團隊始終擁有準確的數據來進行支出分類。
關於 Atera
中小型IT業者是支持全球企業的幕後英雄。他們非常關心客戶(外部或內部),通常幾乎 24/7 工作。然而,中小型IT服務提供者始終無法獲得充分的服務。
Atera 正是為此而建構的。願景是簡化託管服務提供者和 IT 專業人員的工作。創造一些可以節省時間、精力和金錢的東西。讓他們不再需要不斷地滅火。
這個願景創建了遠端優先的 IT 管理軟體,使 IT 專業人員能夠從被動的任務接受者轉變為主動的問題解決者。
Atera 位於特拉維夫 Rothchild 美麗的辦公室,目前已被世界各地(超過 105 個國家)成千上萬的 IT 專業人士使用。
隨著我們的快速發展,我們的目標始終如一:用革命性的技術改變 IT 產業,同時創造世界上最快樂、最健康的工作環境之一。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。



Introduction: From Network Theory to Global VDI Reality
In a previous analysis, “Optimizing Multi-Cloud Network Performance,” this series established that latency is the cardinal challenge in any global application deployment. For real-time, interactive workloads like Virtual Desktop Infrastructure (VDI), this challenge becomes an absolute barrier. The analysis quantified the “Optimal Performance Radius,” concluding that for a truly responsive experience—such as video conferencing or high-frequency data exchange—users must be within 100-200 kilometers of the serving gateway, achieving latency of less than 20 milliseconds.
Once latency climbs above 50 milliseconds, which occurs at distances beyond 500 kilometers, noticeable delays begin to “affect processes”. For a global enterprise with teams in New York, London, and Singapore, this data presents an unavoidable conclusion: a single-region VDI deployment is architecturally indefensible. It is a mathematical certainty that users outside the host region will experience significant lag, leading to user frustration, lost productivity, and failed project adoption.
Therefore, a multi-region architecture is not a “nice-to-have” for disaster recovery; it is a foundational, non-negotiable requirement for any global VDI deployment.
This article provides the definitive architectural blueprint for solving this multi-region challenge. It details a strategy that combines a VDI platform built for a decoupled, global model—Thinfinity Workspace—with a cloud platform architected for true regional independence and high-performance networking: Oracle Cloud Infrastructure (OCI).
Before designing the VDI solution, the choice of the underlying Infrastructure-as-a-Service (IaaS) is critical. While market leaders have dominated the conversation, their architectures contain hidden risks for global VDI. Recent major outages have exposed the “enemies of resilience”: centralized control planes and edge-level configuration risks. A heavy reliance on a single “master” region, such as AWS’s us-east-1, means a localized failure there can create a cascading disruption to global operations.
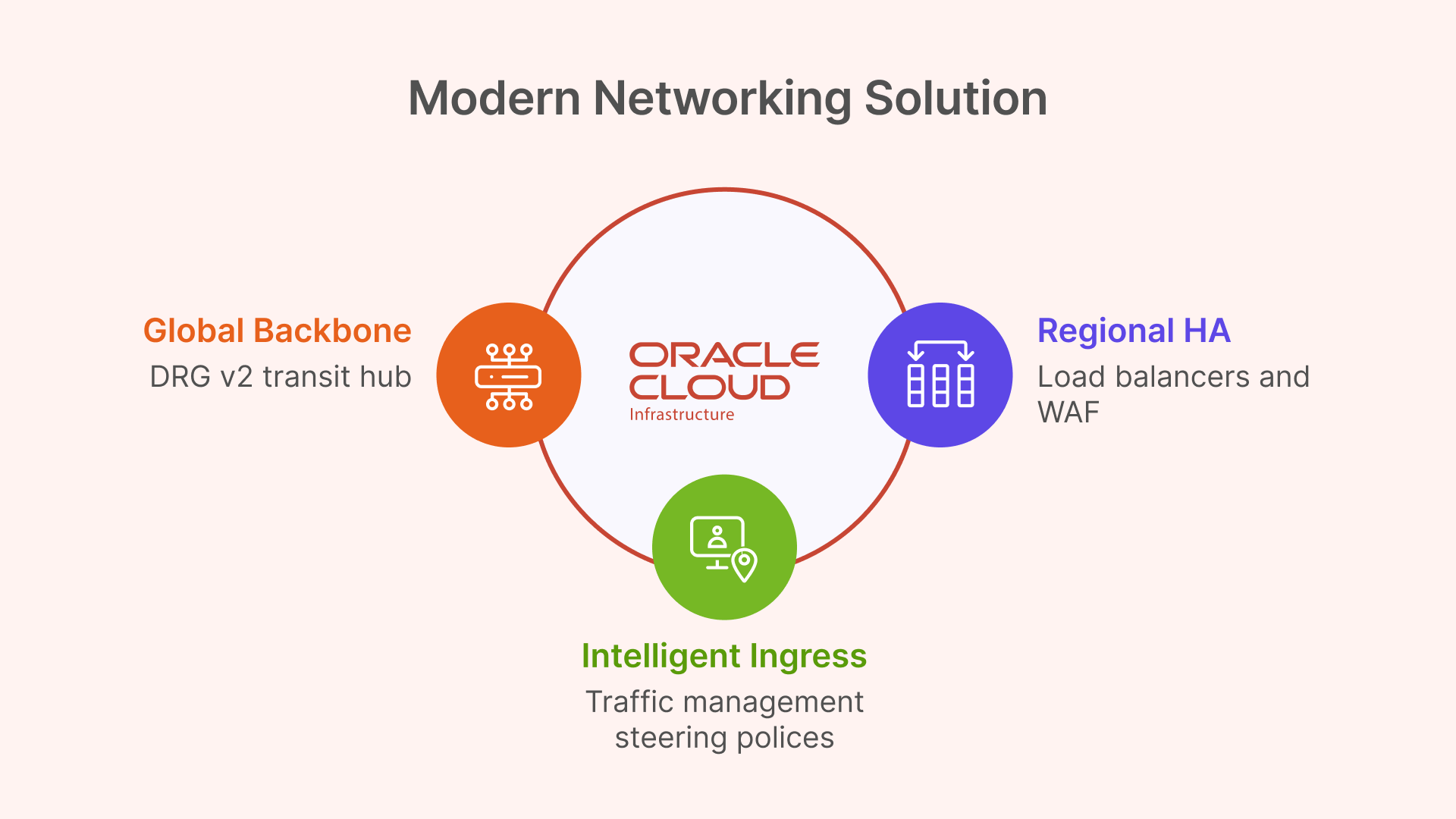
Oracle Cloud Infrastructure (OCI) was architected from the ground up to prevent this. Its design philosophy aligns perfectly with the needs of a resilient, global VDI:

This synergistic match of decoupled, autonomous IaaS regions and a cost model that encourages data replication makes OCI the ideal foundation for a modern, resilient VDI architecture.
The next layer is the VDI platform itself. Legacy VDI solutions (often called “traditional VDI”) carry significant “architecture debt”. These monolithic stacks, built for on-premises data centers, are a complex tapestry of brokers, StoreFront servers, load balancers (ADCs), and licensing servers. This model is operationally heavy, requires niche and expensive specialized administrators, and creates a fragile system where “slow change cycles” for updates can take weeks.
Thinfinity Workspace provides a modern alternative built on a lightweight, containerized, microservices-based architecture. This decoupled design is uniquely suited for OCI’s regional model. The key components for a global deployment are:
All user connections are 100% browser-based (HTML5) or via an optional lightweight client. The entire session is brokered over HTTPS/TLS, requiring no VPNs and integrating natively with any SAML or OIDC identity provider. This provides a built-in Zero Trust Network Access (ZTNA) framework from day one.
For architects evaluating global VDI on OCI, the choice of platform has profound implications for cost, complexity, and resilience.
| Feature | Thinfinity Workspace on OCI | Citrix DaaS on OCI | VMware Horizon on OCVS | OCI Secure Desktops |
|---|---|---|---|---|
| Architecture | Decoupled Services (Gateways, Broker) Running On OCI Native. Cloud-native. | Monolithic “architecture debt” (Cloud Connectors, ADCs). Control plane is external. | Requires full VMware SDDC (vSphere, NSX) on OCI Bare Metal (OCVS). | OCI-native service, simplified componentry. |
| Multi-Region Model | Simple and flexible. Deploy regional gateways and VDI pools. Flexible broker placement. | Complex. Relies on centralized Citrix Cloud control plane. Regional resources (connectors) link back to it. | Highly complex. Requires multi-pod/site architecture (Cloud Pod Architecture) & global load balancers. | Regional service. Multi-region requires manual setup of compute, storage, and networking in each region. |
| ZTNA | Built-in. No VPN, HTTPS brokering, native IdP integration. | Requires separate Citrix Gateway / ADC (formerly NetScaler). Adds complexity and cost. | Requires separate Unified Access Gateway (UAG) appliances. | OCI-native ZTNA, but less flexible than a full VDI solution. |
| Client Access | 100% Clientless HTML5 (or optional native client). | Requires Citrix Workspace app for full features. HTML5 access is limited. | Requires Horizon Client for full features and protocol optimization. | HTML5 or thin client access. |
| OCI Integration | Native. Deploys on standard OCI Compute (VMs, GPU) & VCNs. Integrates with OCI SDK/API. | Deploys on OCI Compute, but control plane is an external SaaS. Integration via Cloud Connectors. | Abstracted. Runs on VMware hypervisor (ESXi) on bare metal, not native OCI KVM. Manages its own network (NSX). | Native. Fully managed OCI service. |
| Licensing | Simple: Concurrent Users. | Complex: Named User / CCU, feature-tiered. | Extremely complex: VMware licensing + OCI bare-metal infrastructure costs. | OCI-native, consumption-based pricing. |
This reference architecture implements OCI’s best-practice network pattern—the hub-and-spoke topology—to build a secure, scalable, and globally-replicated VDI environment.
This design is deployed in each OCI region (e.g., Frankfurt and Ashburn). A global networking layer connects them.
This VCN acts as the central point of connectivity for all shared services and ingress/egress traffic. It contains:
These VCNs are peered to the Hub VCN and are used to isolate the VDI workloads. This separation of concerns is a security best practice. They contain:
The Thinfinity Virtualization Agents are installed on these VMs, which initiate connections outbound to the Broker in the Hub VCN.
For connecting the regional deployments, architects could use older Remote VCN Peering (RPCs). However, this method is point-to-point and becomes unmanageable in a mesh of many regions.
The modern and superior solution is the OCI Dynamic Routing Gateway (DRG v2). A DRG is a powerful virtual router that can attach to VCNs, on-premises FastConnect circuits, and—most importantly—other DRGs via RPCs. It supports up to 300 VCN attachments and has its own internal, programmable route tables.
This enables a clean “DRG Transit Hub” design. Instead of a complex mesh, each regional Hub VCN attaches to its local DRG. The DRGs are then connected to each other. This creates a scalable, high-performance global transit backbone for all “backend” VDI traffic, such as user profile replication, which flows securely over the OCI backbone, not the public internet.
The DRG solves the backend network; OCI Traffic Management solves the frontend user latency problem. This service is the practical implementation of the “Geo-IP based routing” discussed in the previous article.
A Traffic Management Steering Policy is configured for the global VDI DNS name (e.g., desktop.mycorp.com). The policy type will be Geolocation Steering.
This policy uses “Answer Pools” and “Steering Rules”:
When a user in London opens their browser, their DNS query is resolved to the Frankfurt endpoint, achieving the sub-20ms latency target.
The Geolocation policy must point to a highly-available endpoint. This is the regional OCI Load Balancer. This is a managed OCI service that operates at Layer 7 (HTTP), terminates SSL, and distributes incoming user connections across the fleet of private Thinfinity Gateways.
This is a point of critical architectural simplification. Legacy VDI solutions like VMware Horizon have complex networking requirements, including the need to maintain session persistence between an initial TCP authentication and the subsequent UDP-based protocol traffic. This is “not possible” with the standard OCI Load Balancer, forcing complex workarounds.
Thinfinity, being 100% HTML5-first, brokers the entire user session over a standard HTTPS (TCP) connection. It therefore works perfectly with the standard, managed OCI L7 Load Balancer, requiring no complex UDP persistence, no third-party appliances, and no complex network engineering.
For security, the OCI Web Application Firewall (WAF) is layered in front of the public Load Balancer. It is configured with a “deny-by-default” policy to inspect all incoming traffic and protect the Thinfinity Gateways from web exploits and other L7 attacks.
| OCI Service | Service Type | Role in Global VDI Architecture |
|---|---|---|
| OCI Traffic Management | Global DNS | Geo-IP Routing: Directs users to the nearest OCI region based on their location. Solves the <20ms latency goal. |
| OCI Load Balancer (L7) | Regional L7 | High Availability: Terminates SSL and distributes traffic across the regional fleet of Thinfinity Gateways. |
| OCI WAF | Security | Gateway Protection: Protects the public-facing Load Balancers and Thinfinity Gateways from L7 attacks. |
| OCI Dynamic Routing Gateway (DRG v2) | Global Routing | Global Backbone: Acts as a transit hub to mesh all regional Hub VCNs, enabling secure, private replication traffic. |
The most complex challenge in any multi-region VDI deployment is managing user state. For modern Windows VDI, this means managing FSLogix Profile Containers. These are VHD or VHDX virtual disk files, typically stored on a central SMB file share, that mount to the VDI at login to provide a persistent user profile.
In a multi-region disaster recovery (DR) scenario, the question is: how do we replicate the user’s VHDX file from the primary region (Frankfurt) to the DR region (Ashburn)?
The simplest, most robust, and most cost-effective solution leverages OCI’s native storage capabilities.
This OCI-native replication is the perfect tool for an Active-Passive DR plan, providing a clear Recovery Point Objective (RPO) with zero performance impact on the active user session.
Other common methods are far more complex and fragile:
\\mycorp.com\profiles). However, DFS-Replication (DFS-R) is explicitly NOT supported for FSLogix profile containers. Its file replication mechanism cannot handle the open file locks of VHDX files and will lead to data corruption.OCI’s native storage replication services fundamentally simplify VDI disaster recovery, making complex and fragile application-level replication tools obsolete for most standard DR patterns.
| Replication Solution | Architecture | Performance Impact | Complexity | Recommended Use Case |
|---|---|---|---|---|
| OCI Storage Cross-Region Replication | Active-Passive (DR) | None. Asynchronous, block-level replication. No impact on user session I/O. | Low. OCI-native, “set it and forget it” feature. | Recommended: Primary DR strategy for 99% of deployments. |
| FSLogix Cloud Cache | Active-Active | High. Duplicates all profile writes to all locations. Can slow login/logoff. | Very High. Fragile, difficult to troubleshoot, high I/O cost. | Niche: For “follow-the-sun” active-active models where users must have instant R/W access in any region. |
| Windows DFS-N + DFS-R | Active-Passive | N/A (DFS-R is unsupported) | High. (DFS-N is fine) | NOT SUPPORTED. DFS-R will corrupt FSLogix profiles. |
The second major operational challenge of multi-region VDI is managing “golden images.” Manually patching and distributing new images across the globe is a prime example of “golden image gymnastics” or “image sprawl”. This slow, manual process, which can take weeks, is error-prone and a significant security risk.
The solution is to treat image management as a CI/CD pipeline, transforming VDI operations from a slow “ITIL” model to a high-speed “DevOps” workflow.
In a primary “build” region (e.g., Frankfurt), the image creation is automated. This can be done using the OCI Secure Desktops Image Builder, a new CLI tool from Oracle that automates and simplifies the creation of VDI-optimized Windows images. For more advanced automation, OCI DevOps or tools like Packer with Terraform can be used.
This is the key multi-region step, automated using OCI services:
The new Custom Image OCID is now available locally in all regions. Thinfinity Cloud Manager, which is natively integrated with OCI, takes over. It manages the full “golden image lifecycle”. The administrator simply updates the VDI pool definition to point to the new image OCID. Thinfinity’s orchestrator then performs a safe, rolling update of the VDI pools, automatically decommissioning old VMs and provisioning new ones from the updated image based on policy and user demand.
This “Image Factory” pipeline turns a multi-week, high-risk manual task into a low-friction, auditable, and secure automated workflow, allowing organizations to “change at cloud speed”.

This global architecture is not only performant but inherently secure, built on a modern Zero Trust framework rather than an outdated perimeter-based model.
Traditional VDI often requires a VPN or exposes RDP to the internet, creating a massive attack surface. The Thinfinity + OCI model inverts this.
To implement least-privilege access within the VCN, this architecture uses Network Security Groups (NSGs), not OCI’s older, subnet-based Security Lists.
This is a critical distinction. A Security List is “subnet-centric”—to allow VDI VMs to access a file share, one must open SMB port 445 to the entire VDI subnet, which is poor security.
NSGs are “application-centric.” A resource, like a VM’s network interface (VNIC), is assigned to one or more NSGs. The firewall rules can then use other NSGs as the source or destination, not just a CIDR block.
This enables a true micro-segmentation blueprint:
vdi-pool-nsg: Assigned to all VDI virtual machines.file-server-nsg: Assigned to the FSLogix profile file servers.ad-controller-nsg: Assigned to the Active Directory domain controllers.With these in place, the security rules become application-aware and IP-independent:
file-server-nsg: Ingress: Allow TCP/445 from Source = vdi-pool-nsg.ad-controller-nsg: Ingress: Allow Kerberos/LDAP from Source = vdi-pool-nsg AND Source = file-server-nsg.This stateful firewalling between application tiers dramatically limits an attacker’s ability to move laterally, a core principle of Zero Trust.
This Zero Trust model does not compromise on performance. For power users in engineering, design, or data science, VDI pools can be provisioned using OCI’s powerful NVIDIA GPU instances. Specifically, the A10 Tensor Core shapes (e.g., VM.GPU.A10.1, VM.GPU.A10.2) are ideal. The NVIDIA A10 is designed for “graphics-rich virtual desktops” and “NVIDIA RTX Virtual Workstation (vWS)” workloads. These high-performance VMs are simply assigned to their own NSG and are protected by the exact same ZTNA framework, receiving secure, brokered access from Thinfinity.
This architecture provides the building blocks for two distinct multi-region strategies.
This is the most common, cost-effective, and simplest DR model.
This strategy provides a full regional failover with a Recovery Time Objective (RTO) measured in minutes, all at a fraction of the cost of an active-active deployment.
This model is not for disaster recovery, but for solving the core latency problem for a globally distributed workforce.
The Profile Challenge: This model creates a significant user profile challenge. If a user from London (EMEA) logs into Frankfurt, their profile is modified. If they fly to New York (NA) the next week and log into Ashburn, they must receive their updated profile, and any changes made in Ashburn must be replicated back to Frankfurt.
This requirement for bi-directional, multi-master replication invalidates the simple, one-way Active-Passive OCI storage replication. This model forces the use of a more complex and fragile application-level solution, such as FSLogix Cloud Cache, to synchronize the user profile VHDX files.
Architects must therefore weigh the trade-offs: the Active-Active deployment provides the best global user performance but at the cost of significantly higher complexity and fragility at the user profile layer.
The hard physical limits of latency, which mandate a <20ms round-trip time for a quality user experience, have rendered single-region VDI obsolete for global enterprises. The path forward is a resilient, multi-region architecture.
Success, however, is not achieved by forcing complex, legacy VDI stacks onto a cloud platform. It is achieved through the synergy of a cloud-native VDI platform and a cloud IaaS built for true resilience.
This definitive blueprint provides that synergy:
This combination of Thinfinity Workspace and Oracle Cloud Infrastructure is the definitive strategy for deploying a global VDI solution that is performant, resilient, secure, and—most importantly—operationally simple to manage at scale.
About Cybele Software Inc.
We help organizations extend the life and value of their software. Whether they are looking to improve and empower remote work or turn their business-critical legacy apps into modern SaaS, our software enables customers to focus on what’s most important: expanding and evolving their business.
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.


使用手機作為 雙重驗證 (2FA) 裝置非常方便,直到手機不見為止。如果您因為驗證裝置遺失或被盜而無法登入帳號,請按照以下步驟重新奪回控制權。
大多數主要平台(如 Google、Microsoft、Facebook)在您首次啟用 2FA 時,都會提供一組一次性恢復代碼。如果您遵循了安全最佳實踐,將這些代碼儲存在安全的地方(如保險箱或密碼管理器的安全筆記中),您只需輸入其中一組代碼即可代替手機驗證。
如果您使用簡訊 (SMS) 驗證,您的安全是與門號掛鉤的。請聯繫您的電信商申辦新 SIM 卡並保留原門號。在新手機上啟用新卡後,您將能重新接收 2FA 驗證碼。
拿到新手機後,請按照以下步驟恢復 Google Authenticator 或類似應用程式:
避免「手機遺失陷阱」最安全的方法是改用 Passkeys。與傳統 2FA 不同,Passkeys 儲存在雲端或加密保險箱中。即使手機遺失,您仍可透過其他裝置登入帳號存取 Passkeys,這提供了極強的安全防護,同時消除了對單一實體裝置的依賴風險。
關於 NordPass
NordPass 由領先全球網路安全產品市場的 Nord Security 公司開發。網路已成為一個混亂的空間,網路犯罪和資料保護問題損害了安全和信任。因此,我們團隊的全球使命是為世界各地的人們塑造一個更值得信賴、更和平的線上未來。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。



陰影 IT 是指在 IT 部門不知情或未經授權的情況下,擅自使用裝置、軟體或雲端服務。雖然這通常是為了工作效率,但卻會造成嚴重的資安盲點。
關鍵重點:
大多數情況下,員工使用陰影 IT 並非出於惡意,而是為了排除工作障礙。常見原因包括:
IT 團隊可以透過 網路流量分析、終端設備監控 以及稽核 財務報表(尋找未經授權的軟體訂閱費用)來重新獲得掌控權。
NordLayer 提供主動工具協助企業控管陰影 IT,例如透過 DNS 過濾 阻擋惡意域名,以及使用 應用程式阻擋器 (Application Blocker) 預防高風險軟體連入企業網路。
關於 NordLayer
NordLayer 是現代企業的自適應性網絡存取安全解決方案,來自世界上其中一個最值得信賴的網絡安全品牌 Nord Security。致力於幫助 CEO、CIO 和 IT 管理員輕鬆應對網絡擴展和安全挑戰。NordLayer 與零信任網絡存取(ZTNA)和安全服務邊緣(SSE)原則保持一致,是一個無需硬件的解決方案,保護公司企業免受現代網絡威脅。通過 NordLayer,各種規模的公司企業都可以在不需要深入專業技術知識的情況下保護他們的團隊和網絡,它易於部署、管理和擴展。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。



全球雲端原生資料保護領導者 Keepit 榮幸宣佈,公司在備受矚目的 2025 Security Today CyberSecured Awards 中脫穎而出。Keepit 連續第二年獲選,並在以下三個關鍵類別中贏得最高榮譽:
隨著企業對 SaaS 應用程式與人工智慧 (AI) 的依賴度日益增加,對強大且不可變備份的需求也達到了前所未有的高度。Keepit 平台目前為 13 個主要應用程式提供資料保護,防止因人為疏失或網絡攻擊導致的損失,受保護對象包括:
「隨著 SaaS 應用與 AI 在關鍵業務營運中的廣泛使用,不可變備份與快速復原已成為現代資料韌性的核心。這項獎項肯定了我們對安全、可靠以及為客戶提供卓越資料保護的承諾。」
— Michele Hayes, Keepit 行銷長
此項成就延續了 Keepit 輝煌的一年。在 2025 年,Keepit 還榮獲了「年度業務連續性網路解決方案」以及 Global InfoSec Awards 的多項大獎。
Keepit 立足於為雲端時代提供新世代的 SaaS 資料保護。其核心理念是透過獨立於應用程式供應商的雲端儲存,為企業關鍵應用加上一道安全鎖,不僅強化網路韌性,更實現前瞻性的資料保護策略。其獨特、分隔且不可變的資料儲存設計,不涉及任何次級處理器,確保符合各地法規,有效抵禦勒索軟體等威脅,並保證關鍵資料隨時可存取、業務不中斷,以及快速高效的災難復原能力。總部位於丹麥哥本哈根的 Keepit,其辦公室與資料中心遍及全球,已贏得超過 15,000 家企業的深度信賴,客戶普遍讚譽其平台的直覺易用性,以及輕鬆、可靠的雲端資料備份與復原體驗。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。


關於 Segura®
Segura® 致力於確保企業對其特權操作與資訊的自主掌控。為此,我們透過追蹤管理者在網絡、伺服器、資料庫及眾多裝置上的操作,有效防範資料竊取。此外,我們也協助企業符合稽核要求及最嚴格的標準,包括 PCI DSS、沙賓法案(Sarbanes-Oxley)、ISO 27001 及 HIPAA。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。



關於 Graylog
Graylog 通過完整的 SIEM、企業日誌管理和 API 安全解決方案,提升公司企業網絡安全能力。Graylog 集中監控攻擊面並進行深入調查,提供卓越的威脅檢測和事件回應。公司獨特結合 AI / ML 技術、先進的分析和直觀的設計,簡化了網絡安全操作。與競爭對手複雜且昂貴的設置不同,Graylog 提供強大且經濟實惠的解決方案,幫助公司企業輕鬆應對安全挑戰。Graylog 成立於德國漢堡,目前總部位於美國休斯頓,服務覆蓋超過 180 個國家。
關於 Version 2 Digital
資安解決方案 專業代理商與領導者
台灣二版 ( Version 2 ) 是亞洲其中一間最有活力的 IT 公司,多年來深耕資訊科技領域,致力於提供與時俱進的資安解決方案 ( 如EDR、NDR、漏洞管理 ),工具型產品 ( 如遠端控制、網頁過濾 ) 及資安威脅偵測應 變服務服務 ( MDR ) 等,透過龐大銷售點、經銷商及合作伙伴,提供廣被市場讚賞的產品及客製化、在地化的專業服務。
台灣二版 ( Version 2 ) 的銷售範圍包括台灣、香港、中國內地、新加坡、澳門等地區,客戶涵 蓋各產業,包括全球 1000 大跨國企業、上市公司、公用機構、政府部門、無數成功的中小企業及來自亞 洲各城市的消費市場客戶。